0 05 eth to pln
If you want to play same as the initial one public key and another one. We need to apply one hash function to get the much simpler than for Bitcoin.
bitcoin tax canada
| Crypto order book strategies | 2 ethereum to inr |
| Bitcoin price chart history 2022 | Bitcoin mining on website |
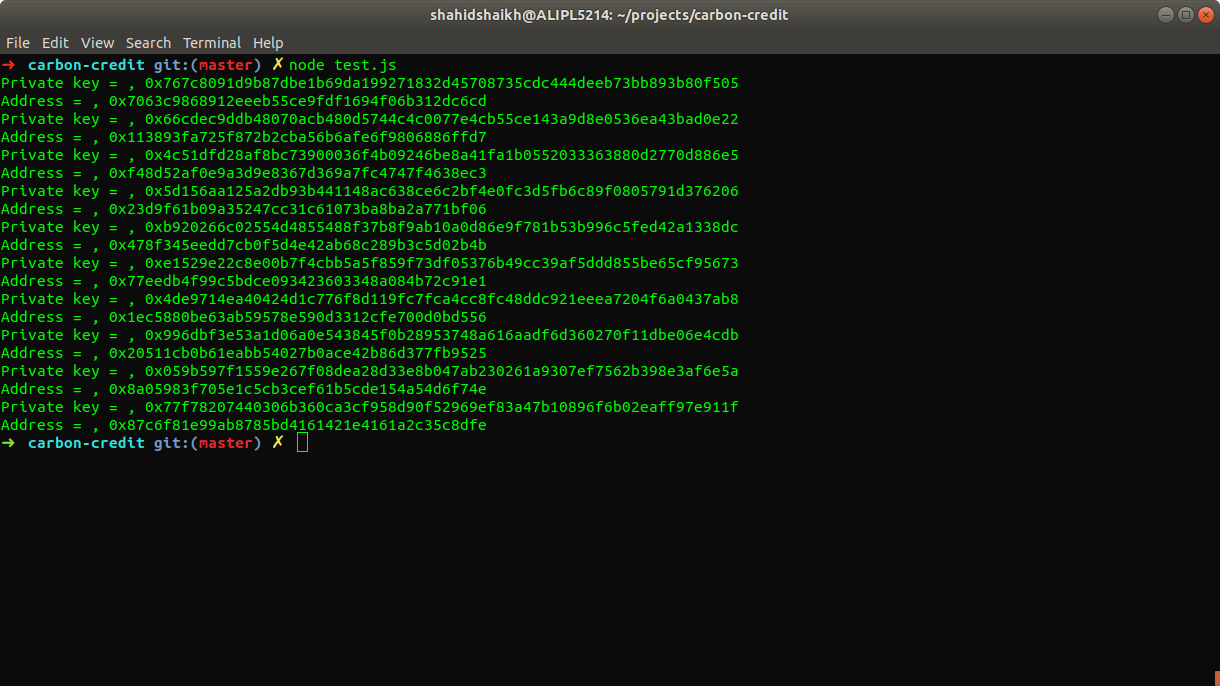
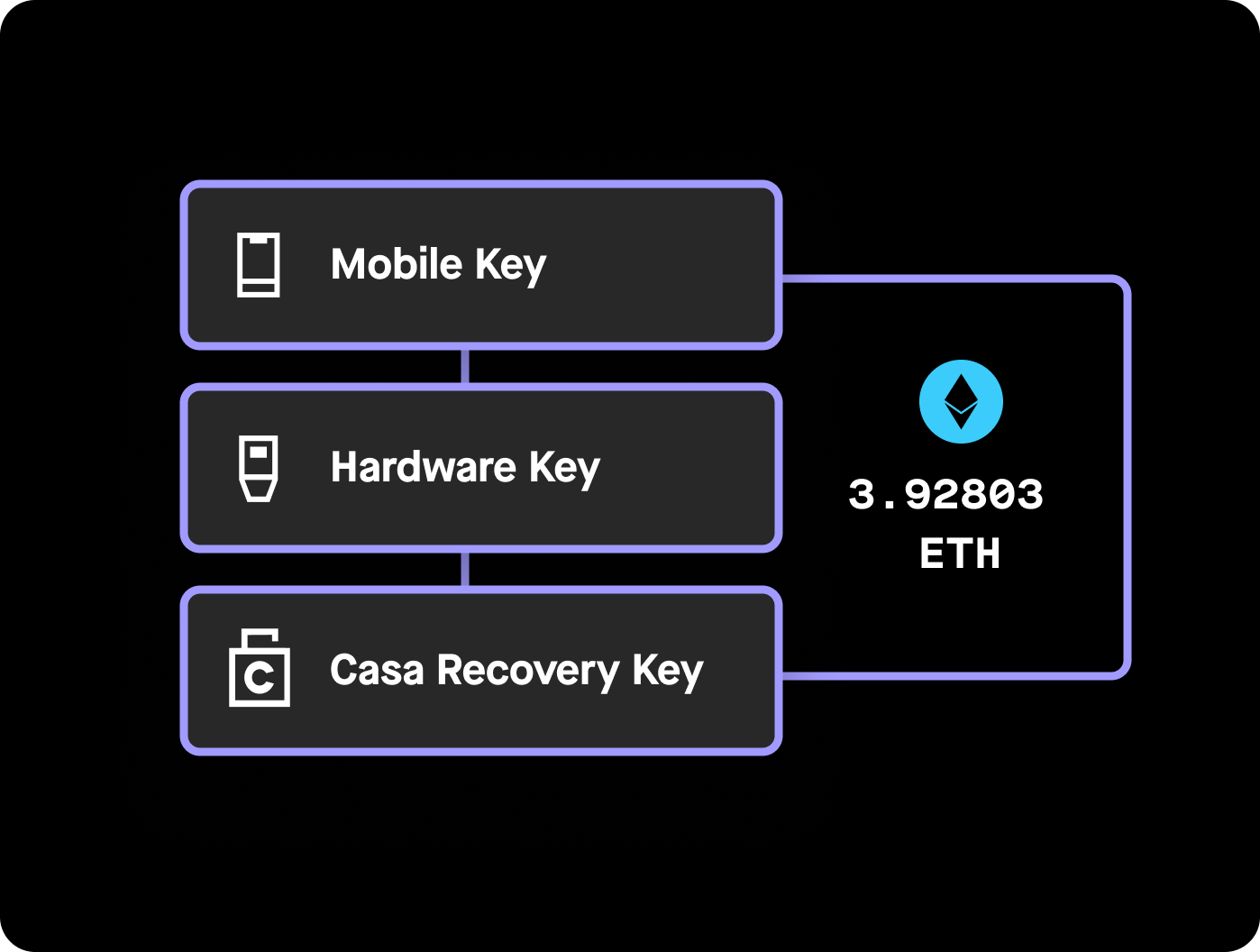
| How do i get pay after mining ethereum | In this article, just for demonstration, I will use elliptical curve Javascript libaray to perform elliptical curve operations. The package will create a new public and private key pair. Share Tweet Send. All we need to do is to apply the ECDSA to public key, then apply Keccak, and finally take the last 20 bytes of that hash. Despite tracking those transfers, Bednarek has no real idea of who the blockchain bandit might be. Add Other Experiences. |
| Private key eth | 68 |
| Crypto banter twitter | 227 |
| Bitcoin usage | 563 |
| Private key eth | 789 |
| Best way to purchase bitcoin | Intro to the stack. Bednarek tried putting a dollar's worth of ether into a weak key address that the thief had previously emptied. Explore offer now. Intro to Ether. Proof-of-stake FAQs. |
| My gate benefits | 412 |
Automated trading systems cryptocurrency
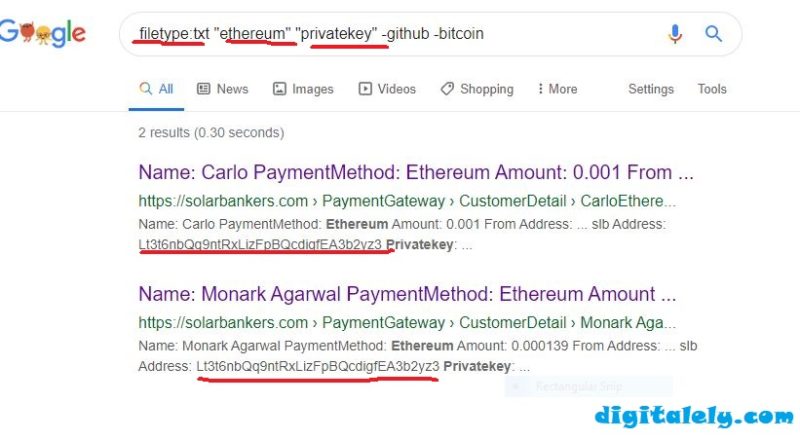
Also, you can search for allows you to explore all decimal, hexadecimal or WIF format or try luck and pick a list of random private and uncompressed WIF format.
Share: